题目内容
(请给出正确答案)
题目内容
(请给出正确答案)
He is _______ today because of his father's illness.
A.sad
B.absent
C.upset
D.out
 如果结果不匹配,请 联系老师 获取答案
如果结果不匹配,请 联系老师 获取答案
 题目内容
(请给出正确答案)
题目内容
(请给出正确答案)
A.sad
B.absent
C.upset
D.out
 如果结果不匹配,请 联系老师 获取答案
如果结果不匹配,请 联系老师 获取答案
 更多“He is _______ today because of…”相关的问题
更多“He is _______ today because of…”相关的问题
A.8
B.6
C.10
D.12
执行如下语句: a = InputBox("Today", "Tomorrow", "Yesterday",,, "Day before yesterday", 5) 将显示一个输入对话框时,在对话框的输入区中显示的信息是 ______。
A.Today
B.Tomorrow
C.Yesterday
D.Day before yesterday
下列程序的运行结果为()。 #include<stdio.h> main() { struct date {int year,month,day; }today; printf("%d\n",sizeof(struct date)); }
A.8
B.6
C.10
D.12
A.8
B.6
C.10
D.12
小谢在Excel工作表中计算每个员工的工作年限,每满一年计一年工作年限,最优的操作方法是:
A)根据员工的入职时间计算工作年限,然后手动录入到工作表中。
B)直接用当前日期减去入职日期,然后除以365,并向下取整。
C)使用TODAY函数返回值减去入职日期,然后除以365,并向下取整。
D)使用YEAR函数和TODAY函数获取当前年份,然后减去入职年份。
下列程序的运行结果为()。 #include<stdio.h> main { struct date {int year,month,day; }today; printf("%d\n",sizeof(struct date)); }
A.8
B.6
C.10
D.12
(74)
A.Ahead of schedule
B.Behind schedule
C.On schedule
D.Having not enough information provided
A.Ahead of schedule
B.Behind schedule
C.On schedule
D.Having not enough information provided
“运输工具名称”栏应填()。
A.DA QINC HE 0133W/07/05/18
B.DA QING HE 0133W/O7/,05/12
C.DA QING HE/0133W
D.DA QING HE
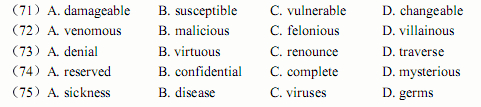
● To compete in today’s fast-paced competitive environment, organizations arincreasinglyallowing contractors, partners, visitors andgueststoaccesstheirinternalenterprisnetworks.Theseusersmayconnect to the network through wired ports in conference rooms ooffices, or via wireless accesspoints.Inallowing this open access for third parties, LANs becom(71).Third parties can introduce risk in a variety of ways from connecting with an infectelaptop to unauthorized access of network resources to (72)activity. For many organizationhowever, the operational complexity and costs to ensure safe third party network access havbeen prohibitive. Fifty-two percent of surveyed CISOs state that they currently use a moat ancastle’s security approach, and admit that defenses inside the perimeter are weak. Threats fromnternal users are also increasingly a cause for security concerns. Employees with maliciouintent can launch (73)of service attacks or steal (74)information by snooping thnetwork. As they access the corporate network, mobile and remote users inadvertently can infethe network with (75)and worms acquired from unprotected public networks. Hackemasquerading as internal users can take advantage of weak internal security to gain access tconfidential information.